Cybersecurity Awareness Training
To thwart cyberattacks, all utility employees must understand the basic good habits that support cybersecurity—what security professionals call cyber hygiene. For this reason, utilities need to educate their employees about potential threats and their roles in preventing them. This education is often called cybersecurity awareness training.
Importance
Cyberattacks often depend on human mistakes to be successful. Many companies and even governments have fallen victim to malware because an unaware employee clicked on an infected email attachment or inserted an infected USB drive into a computer, as was likely the case when Stuxnet entered Iran’s nuclear enrichment facility (Zetter 2014). Cybersecurity awareness training teaches employees to avoid these mistakes. The development of good, safe computer habits (cyber hygiene) can often save an organization time, money, frustration, and reputational damage. Though simple, these habits are extremely effective in closing off vulnerabilities that can give attackers access to utility systems. Research has shown a significant number (19%–36%) of data breaches can be traced to human error (Ponemon Institute 2017).
Intersections With Other Building Blocks
The organizational security policy building block defines objectives for the cybersecurity awareness training building block. Cybersecurity awareness training, which focuses on teaching cyber hygiene to all employees, benefits from workforce development, which provides advanced skills development for technical staff. Those technical professionals can help monitor and coach nontechnical staff, making cybersecurity awareness training more effective.
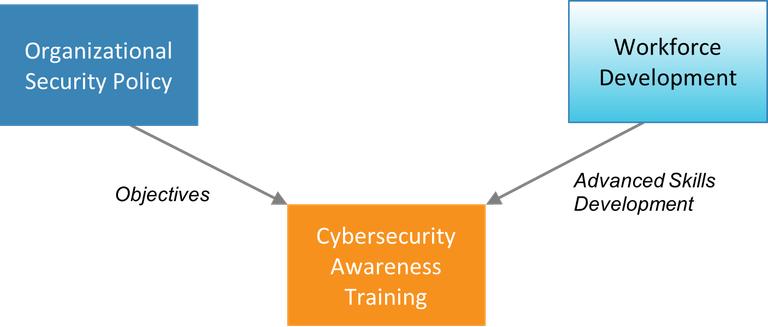
Figure 10. Information passed to the cybersecurity awareness training building block
Process and Actions
Utility staff may believe that responsibility for cybersecurity rests only with the IT department. Staff may not be aware that their actions can impact cybersecurity, or that they have a crucial role to play in keeping cyberattackers off utility computers and networks.
Management must impress on all employees that cybersecurity is an organizational priority and everyone’s responsibility. They must create a corporate culture that emphasizes cybersecurity as a key element of the organization’s success. The utility leadership must commit to building a culture of cybersecurity (Drolet 2019). Staff will be more open to change if they understand that the entire hierarchy values cybersecurity and is making the effort together (Osterman Research 2020).
Cybersecurity awareness training works best when some initial training (e.g., a day-long class on cyber hygiene) is reinforced regularly (Harris and Maymi 2016). Reinforcement may be through follow-up classes or online webinars, quizzes, or social engineering exercises. Social engineering refers to attempts by a cyberattacker to trick employees into cyber-unsafe behavior. One example of this is phishing, in which people are tricked into clicking a malicious link in an email by making that link appear to be legitimate.
The same social engineering tricks used by attackers can also be used within a utility to train staff to resist these tricks (e.g., the utility security staff can phish their fellow employees). The aim of these exercises should be to provide a useful learning exercise for employees to increase their awareness of attempted attacks in the future. Punitive action should be reserved for situations where an employee willfully refuses to follow cyber hygiene guidance or continually proves to be a potential cyber risk (Osterman Research 2020).
Management should incentivize good cybersecurity awareness. Employee cybersecurity errors can usually be addressed through additional education and training; sometimes, just the awareness of internal social engineering exercises is enough to motivate better behavior. Where possible, cybersecurity awareness training should be entertaining, humorous, and easy to understand (Harris and Maymi 2016). The goal is to keep employees engaged long enough that the good cyber habits become a kind of muscle memory (Osterman Research 2020).
Finally, employees’ cybersecurity awareness should be tracked to show awareness of and compliance with expected behaviors over time.
Essential Data
All employees need training at a basic level of cybersecurity awareness. This includes avoidance of phishing, responsible use of removable media (e.g., USB storage devices), and avoidance of unsecured Wi-Fi networks. In addition, some employees need additional training if they regularly handle sensitive information. Sensitive information includes:
- Data about operations and security of the utility
- Personally identifiable information about customers and staff
- Financial information
- Trade secrets
- Any information deemed sensitive by local laws or regulations
- Software licenses
- Details about computer network configurations and other data that would be useful to cyberattackers
- Information that is covered by a nondisclosure agreement signed by the utility.
It is therefore important to know who within the utility has access to sensitive databases and files to determine the type of security training needed. Useful questions to ask when gathering data include:
- For each category of sensitive information, who has access to it?
- How do we track who has access to sensitive information?
- Is there a process for revoking access to sensitive information when the employee no longer needs it or when the employee leaves the organization?
- How sensitive is this information? (What negative impact would arise if it were lost, stolen, or altered by an attacker?)
- What do staff need to know about security for each type of sensitive information and the system that stores it?
Assembling these data will enable utility management to identify the training needs of different members of the staff.
Recommended Reading
Additional Resources and References
Zetter, Kim. 2014. Countdown to Zero Day. New York: Crown Publishers.